Whether you’re a seasoned entrepreneur or a recent graduate, building a strong personal brand is
Recent Posts
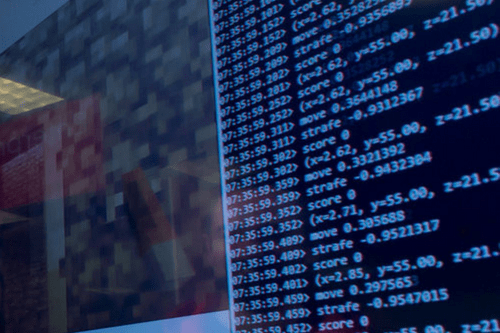
JoinPD.com is the key that opens the immersive world of Pear Deck, a platform that
There is a fascinating and inspiring journey behind the success of Steve Harvey. A story
Best known for being a child model, Dannielynn Birkhead is the daughter of Anna Nicole
Hey there, financial explorers! Today, let’s dive into the fascinating world of life insurance and
Lil Man J from the United States of America born on 17th June 2005 began
Life is so great when you get to meet people who inspire you in life.
Richard Montañez, a man who never let a broken Cheetos machine stop him from achieving
Ah, the language of flowers, an ancient art that speaks volumes without uttering a single
Alexandra Daddario is a beautiful and talented force to be reckoned with in the entertainment